From pv magazine 11/2021
Since the turn of the millennium, when utilities first felt the strain of a sudden rise in distributed energy resources (DERs), technical standards have served to bring industry into consensus around common methods for grid modernisation. For example, in the United States, a breakthrough for renewables came in 2003 with the release of Standard 1547 for interconnecting DERs, published by the Institute of Electrical and Electronics Engineers (IEEE). This influential standard and others like it first established safe and clear practices for DER integration on the electric grid.
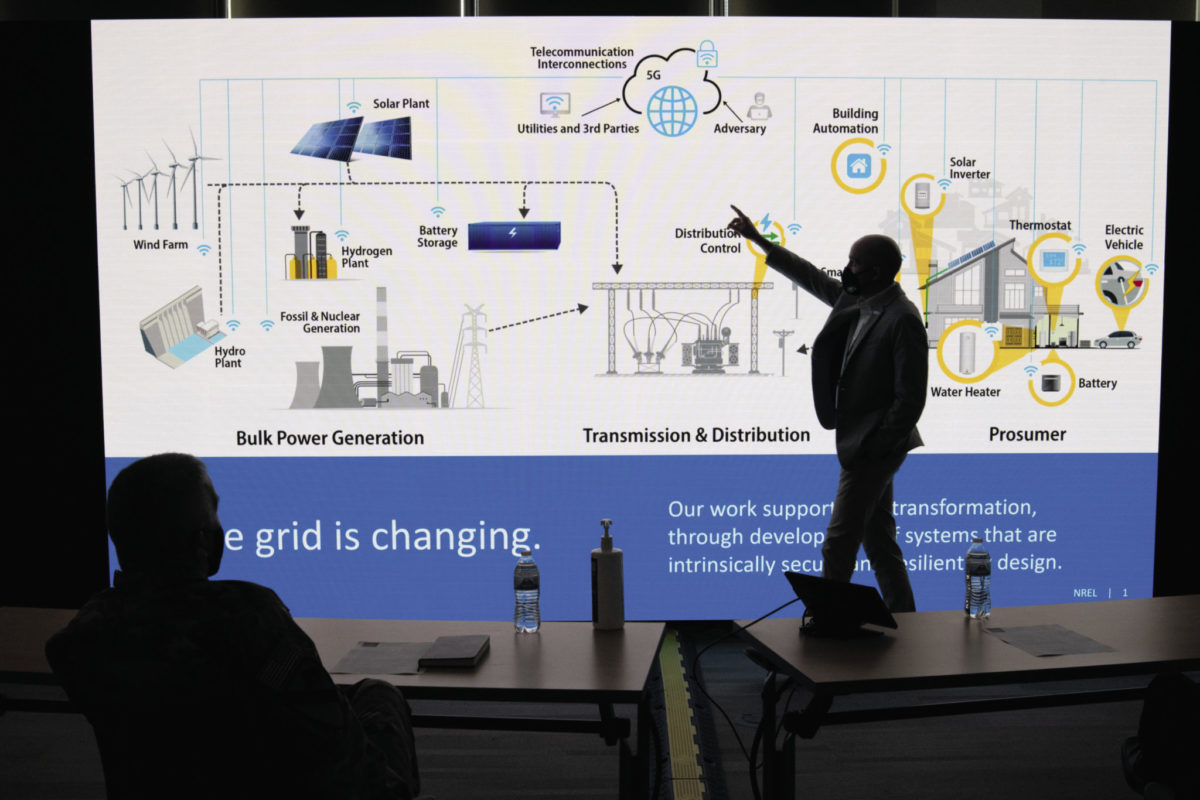
Fast-forward to the present, and the electric industry supports DERs with a well-kept garden of grid modernisation standards, still centred on Standard IEEE 1547, now its 2018 revision. But in the space between standards, cybersecurity creates a special challenge for the industry: New threats and adversaries can appear wherever the grid is unprotected. Adding to the difficulty, cybersecurity is an all-encompassing topic, yet still application-specific. It is critically important, but impossible to perfect.
These circumstances have resulted in an inconsistent standards environment that is too complex for most operators and lacks strong consensus from regulators, leaving many power systems vulnerable at a time when they are integrating even more DERs.
Gaps in guidance
Regarding standards, DER cybersecurity primarily fits into the category of “interoperability,” relating to all communications and controls, data exchange, and system coordination. Still, the relevant guidance is somewhat scattered throughout the standards. For example, IEEE 1547-2018 points to several other standards for communication exchange: IEEE 2030.5, IEEE 1815 (DNP3 protocol), and SunSpec Modbus. These standards provide recommendations around DER communications like encryption and key management, but are far from the full picture for DER security. And gaps are already understood to exist for these interoperability standards, such as their ability to scale to many-DER systems. Meanwhile, IEEE 1547.3 is tasked with monitoring and control of DERs, but only provides the high-level treatment of cybersecurity guidance one might imagine in a 2007 standard (1547.3 is currently under revision). Another standard, International Electrotechnical Commission (IEC) Standard 62351, treats cybersecurity for information and communication technologies, but leaves DER-specific security open to interpretation.
Starting with those named above, there are plenty of guides, standards, frameworks and best practices that have kept power systems secured well enough – much of which can be attributed to staff training and best practices among organisations. But, as more DERs enter the power system, inconsistent practices can become susceptible to gaps. Operators need comprehensive guidance that covers all technical, business, and operational security for DERs, but, currently, it can be overwhelming to maintain (or even determine) the best practices for all DER operations.
“There are multiple layers to cybersecurity – if you skip securing even one of these layers, you cannot say the system is holistically secured,” explained Danish Saleem, a National Renewable Energy Laboratory (NREL) engineer who is now serving as the chair of a U.S. national laboratory coordination committee and vice chair for an IEEE 1547.3 working group to support DER and inverter-based resource (IBR) cybersecurity standards and related initiatives.
“DERs involve a vast technical space of communication protocols, user interfaces, software applications, and power controls. Therefore, it is important that we understand each of these layers and how they interact with each other within the DER ecosystem to design intrinsically secure systems,” Saleem said.
Saleem is helping lead IEEE 1547.3 development, which will provide cybersecurity guidelines for one or more DERs interconnected with an electric power system. Unlike its predecessor, the updated IEEE 1547.3 deliberately takes the form of a guide in order to manage ongoing revisions and provide up-to-date security recommendations for DER stakeholders. Once it publishes in late 2021, this guide will clarify the broad requirements of cybersecurity, going beyond the “DER interface” covered by IEEE 1547-2018. Until then, other measures are available to practice advanced cybersecurity today.
Cybersecurity stopgaps
Apart from the standards already listed, new resources are appearing that provide operators a better defence than only a couple years previous.
In the United States, the Biden-Harris administration began with a critical security blitz, spurring the Department of Energy (DOE) to address cybersecurity risks to the electric system in 100 days. Among other achievements, this effort led to an update for the department’s C2M2 (Cybersecurity Capability Maturity Model), which addresses emerging technologies and sophisticated threats, helping industry situate itself in the fast-changing sector. C2M2 was developed with input from 77 organisations in the energy sector and takes the form of a “maturity model,” which emphasises that cybersecurity comes with many layers which organisations can proactively work toward. The update includes the addition of a cybersecurity architecture domain, which helps address OT (operational technology) system architecture for energy systems.
Another tool that provides formal guidance is the DER-Cybersecurity Framework (DER-CF). Considering the complexity that troubles operators, DER-CF provides an online tool to assess cybersecurity posture for distributed energy systems. Originally developed for U.S. federal government agencies, DER-CF is a useful resource for any site reviewing its cybersecurity. For cybersecurity outside of the United States, where power systems can be characteristically different, NREL has recently published a report detailing the building blocks for general power sector cybersecurity, in collaboration with the U.S. Agency for International Development (USAID).
“The cybersecurity space for operators is difficult to navigate, and more-so every day as energy systems become more distributed and digital,” said Tami Reynolds, an NREL researcher who leads the DER-CF effort and other cybersecurity programs. “The cybersecurity tools we are creating help stakeholders become informed about the security of their energy system so that critical decisions can be made to address any gaps that are identified.”
Consensus is also manifesting for DER-specific cybersecurity. A recent NREL report outlines the current cybersecurity environment for electric vehicle operations, summarising how the current standards space relates to real security decisions. A similar report was also published for cybersecurity in photovoltaic plant operations. For the solar industry, a U.S. public-private effort named the Cybersecurity Advisory Team for State Solar is working to circulate current knowledge around solar cybersecurity with education and engagement tools.
For more explicit cybersecurity, NREL has developed a low-cost, plug-and-play technology to protect networks and devices today. Module-OT is a portable software that can be embedded in devices or installed on a hardware microcontroller and performs encryption, key management, authorisation, and other cybersecurity functions. Module-OT is a true stopgap for operational cybersecurity, able to protect legacy systems against advanced threats without disrupting operation or requiring expensive capital buildout. It has also been extensively field-tested on NREL research hardware.
Looking ahead to tomorrow’s cybersecurity resources, the DOE has established advanced research platforms to innovate and validate new solutions. With these capabilities, researchers can play the attack and the defence and show how different scenarios unfold on real power systems.
Future factors
It could go without saying that a system is never perfectly protected. Between the mix of manufacturer DER designs, the split incentives for cybersecurity among energy asset owners, supply chain challenges, and the highly complex challenge in securing millions of devices, there will always be new threats and vulnerabilities. An overall cyber posture that actively practices the best-available security – from how employees interact with devices to system configuration offers the best protection. These practices are identified, validated, and agreed upon through the development and publication of standards.
Connor O’Neil
About the author
Connor O’Neil is a writer at the National Renewable Energy Laboratory. He covers energy technologies and grid modernization.
This content is protected by copyright and may not be reused. If you want to cooperate with us and would like to reuse some of our content, please contact: editors@pv-magazine.com.







1 comment
By submitting this form you agree to pv magazine using your data for the purposes of publishing your comment.
Your personal data will only be disclosed or otherwise transmitted to third parties for the purposes of spam filtering or if this is necessary for technical maintenance of the website. Any other transfer to third parties will not take place unless this is justified on the basis of applicable data protection regulations or if pv magazine is legally obliged to do so.
You may revoke this consent at any time with effect for the future, in which case your personal data will be deleted immediately. Otherwise, your data will be deleted if pv magazine has processed your request or the purpose of data storage is fulfilled.
Further information on data privacy can be found in our Data Protection Policy.